- AnyConnect VPN/ZTNA User and Management Tunnels
- Cisco Secure Endpoint
- Cloud Management Module
- Network Visibility Module
- Umbrella Roaming Security module
- ISE Posture module
- Network Access Manager
- Posture (for Secure Firewall)
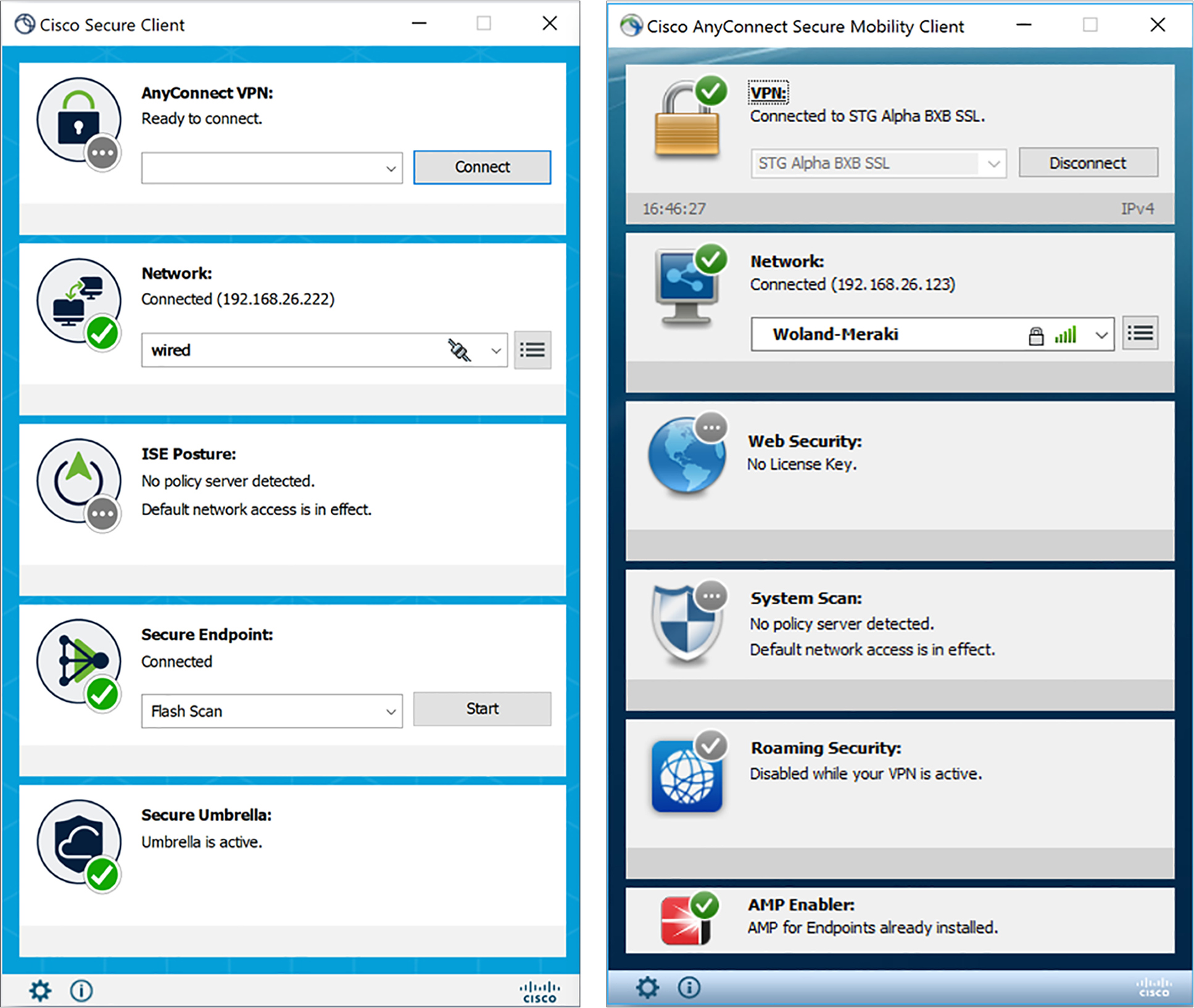
Cisco Secure Client, formerly Cisco AnyConnect Secure Mobility Client, is available for Windows 10 and 11. The user interface will be familiar to current AnyConnect users with some updated branding and iconography.
Customers running on macOS and Linux will continue to utilize AnyConnect 4.x until Cisco Secure Client has full OS support.
Cisco Secure Client is the latest version of one of the most widely deployed security clients. Secure Client is built upon Cisco AnyConnect, which provides Remote Access services and a suite of modular security services.
AnyConnect is now known as Cisco Secure Client. Additionally, Secure Endpoint is a new optional module of Secure Client that provides customers with integrated advanced Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) capabilities.
New users can install Secure Client by traditional methods and customers looking to adopt the new Cloud Management functions can do so with a packaged installer download from the Secure Endpoint portal.
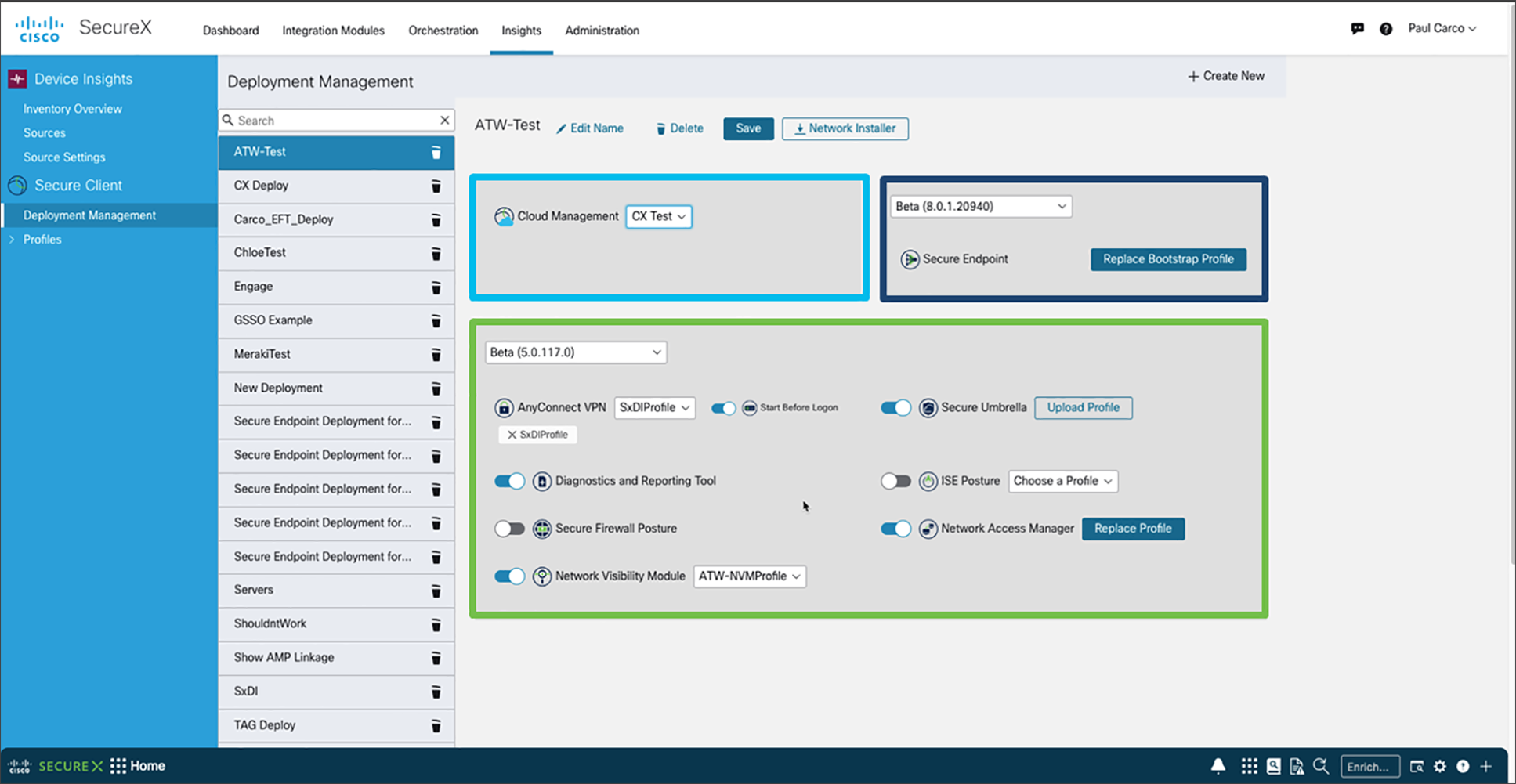
Cloud Management via SecureX with Device Insights is a new optional capability for Secure Client. This new feature makes deploying, configuring, and monitoring Secure Client simple. Customers are not required to adopt cloud management and can continue to deploy using the current mechanisms; Cisco Secure Firewall, ISE, Software Management tools, i.e., SCCM as an example, or directly using the MSI.
New SecureX screens and tools for Cloud Management include:
● Customizing and generating a network installer for Secure Client
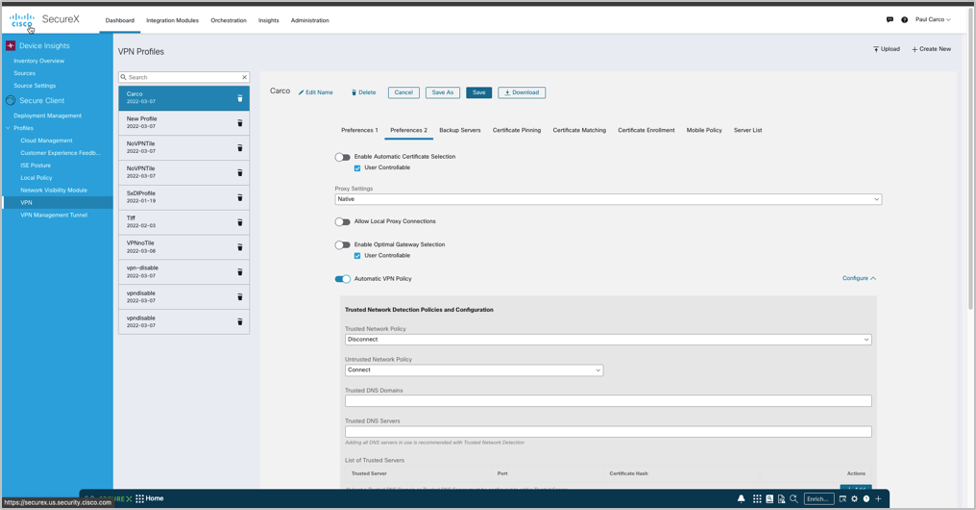
● Creating and downloading custom VPN profiles for Secure Client
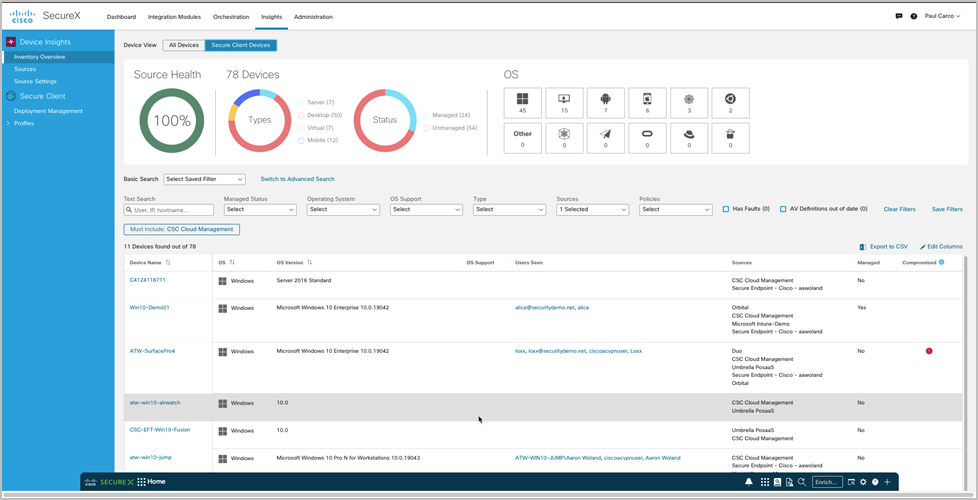
● Integrating with Device Insights to monitor and manage an inventory of endpoints with Secure Client installed
Secure Endpoint Module
Secure Client Modules
Cisco Secure Client provides many options for automatically connecting, reconnecting, or disconnecting VPN sessions. These options offer a convenient way for your users to connect to your VPN and support your network security requirements. An always-on intelligent VPN helps AnyConnect client devices automatically select the optimal network access point and adapt its tunneling protocol to the most efficient method, including Datagram Transport Layer Security (DTLS) protocol for latency-sensitive traffic, and a path for entering Zero Trust Network Access. Tunneling support is also available for IP Security Internet Key Exchange version 2 (IPsec IKEv2). Select application VPN access may be enforced on Apple iOS and Google Android.
Management VPN tunnel provides connectivity to the corporate network whenever the client system is powered up, not just when the end-user establishes a VPN connection. As a result, you can perform patch management on out-of-the-office endpoints, especially devices that are infrequently connected by the user, via VPN, to the office network. This feature will also benefit endpoint OS login scripts that require corporate network connectivity. This capability does not have an end-user interface.
Available with Cisco Secure Client for Windows, Secure Endpoint functions as a module within Cisco Secure Client and is accessible via the Cisco Secure Client user interface. The Cisco Secure Endpoint Cloud can also deploy Cisco Secure Client with Cisco Secure Endpoint, as can SecureX Cloud Management. by taking advantage of this integration, customers can reduce the number of clients under their management.
SecureX Cloud Management Deployment for Cisco Secure Client enables administrators to create cloud-managed deployments of Cisco Secure Client. The deployment configuration generates the option to download a lightweight bootstrapper that contains the information needed by the endpoint to contact the cloud for the specified Cisco Secure Client modules by the deployment with their associated profiles. A full installer is also available. In either case, the installers can be distributed to the endpoints by the administrator using their preferred software method.
The Network Visibility Module delivers a continuous feed of high-value endpoint telemetry, which allows organizations to see endpoint and user behaviors on their networks. It collects flow from endpoints on and off-premises and valuable contexts like users, applications, devices, locations, and destinations. It caches this data and sends it to the Network Visibility Module Collector when it is on a trusted network (the corporate network on-prem or through VPN). Network Visibility Module Collector is a server that receives Internet Protocol Flow Information Export (IPFIX) data and optional filters that are exported to Cisco Secure Network Analytics Endpoint License, Syslog, or a third-party collector. Network Visibility Module Collector processes received messages that adhere to the nvzFlow protocol specification.
NVM sends flow information only when it is on the trusted network. By default, no data is collected. Data is collected only when configured as such in the profile, and the data continues to be collected when the endpoint is connected. If collection is done on an untrusted network, it is cached and sent when the endpoint is on a trusted network. No UI
To take advantage of Umbrella Roaming Security service, you need the Professional, Insights, Platform, or MSP package subscriptions. Umbrella Roaming Security provides DNS-layer security when no VPN is active and adds an Intelligent Proxy. Additionally, Cisco Umbrella subscriptions provide content filtering, multiple policies, robust reporting, functional directory integration, and more. Use the same Umbrella Roaming Security module regardless of the subscription.
ISE Posture is a module you can choose to install as an additional security component of the Cisco Secure Client product. Perform an endpoint posture assessment on any endpoint that fails to satisfy all mandatory requirements and is deemed non-compliant. The other endpoint authorization states are posture unknown or compliant by meeting mandatory requirements. The client receives the posture requirement policy from the headend, collects the posture data, compares the results against the policy, and sends the assessment results back to the headend. Even though ISE determines whether the endpoint is compliant, it relies on Secure Endpoint's policy evaluation.
Network Access Manager manages user and device identity and the network access protocols required for secure access. It works intelligently to prevent end-users from making connections that violate administrator-defined policies. It detects and selects the optimal Layer 2 access network by its policies and performs device authentication for access to both wired and wireless networks.
Secure Firewall Posture performs server-side evaluation where the Secure Firewall asks only for a list of endpoint attributes such as operating system, IP address, registry entries, local certificates, and filenames, and they are returned by Secure Firewall Posture. Based on the policy’s evaluation result, you can control which hosts are allowed to create a remote access connection to the security appliance.
Benefits and Details
Remote-Access VPN/ZTNA
Broad operating system support
Windows 11 (64-bit), current Microsoft supported versions of Windows
10 x86 (32-bit) and x64 (64-bit), and Windows 8
Microsoft-supported versions of Windows 11 for ARM64-based
Microsoft-supported versions of Windows 10 for ARM64-based PCs
Note: Cisco Secure Client 5.0 is Windows 10/11 Only. AnyConnect supports all the above.
macOS 12, 11.2, 10.15, and 10.14 (all 64-bit)
See mobile data sheet for Mobile OS support
Software access
Downloads are available in the Cisco.com Software Center
Technical support and software entitlement for AnyConnect is included with all term-based Plus and Apex licenses, and it can be purchased separately for the Plus perpetual license
The contract number must be linked to Cisco.com ID. See the Secure Client ordering guide for details
Optimized network access: VPN protocol choice SSL
(TLS and DTLS); IPsec IKEv2
AnyConnect provides a choice of VPN protocols, so administrators can use whichever protocol best fits their business needs
Tunneling support includes SSL (TLS 1.2 and DTLS 1.2) and next-generation IPsec IKEv2
DTLS provides an optimized connection for latency-sensitive traffic, such as VoIP traffic or TCP-based application access
TLS 1.2 (HTTP over TLS or SSL) helps ensure availability of network connectivity through locked-down environments, including those using web proxy servers
IPsec IKEv2 provides an optimized connection for latency-sensitive traffic when security policies require use of IPsec
Optimal gateway selection
Determines and establishes connectivity to the optimal network-access point, eliminating the need for end users to determine the nearest location
Mobility friendly
Designed for mobile users
Can be configured so that the VPN connection remains established during IP address changes, loss of connectivity, or hibernation or standby
With Trusted Network Detection, the VPN connection can automatically disconnect when an end user is in the office and connect when a user is at a remote location
TLS/DTLS 1.2 strong ciphers supported
Next-generation encryption, including NSA Suite B algorithms, ESPv3 with IKEv2, 4096-bit RSA keys, Diffie-Hellman group 24, and enhanced SHA2 (SHA-256 and SHA-384). Applies only to IPsec IKEv2 connections. Premier (formerly AnyConnect Apex) is required
Wide range of deployment options
Deployment options:
Predeploy—New installations and upgrades are done either by the end user or by using an enterprise Software Management System (SMS)
Web Deploy—The Cisco Secure Client package is loaded on the headend, which is either a Secure Firewall ASA, Secure Firewall Threat Defense, or an ISE server. When the user connects to a firewall or to ISE, Cisco Secure Client is deployed to the client
SecureX Cloud Management Deployment— Cisco Secure Client 5.0 can be deployed from the Cloud using customizable deployments
Wide range of authentication options
SAML 2.0 with Embedded or Native Browser (SSO)